-
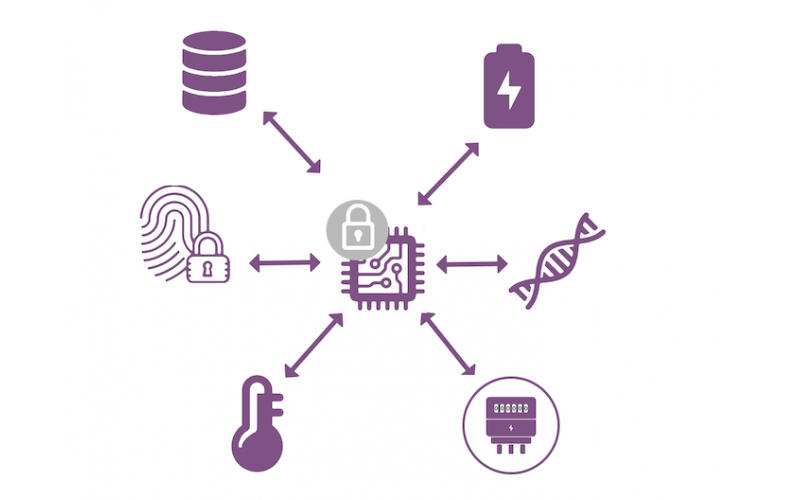
Java Card for the Internet of Things : Trusted Peripherals
The release of the Java Card 3.1 specification has helped to simplify the implementation of Trusted Peripheral use cases and will enable trust and the exchange of sensitive data at the very edge. Find out how Java Card secures the “last yard” between devices and attached peripherals
2021/07/19 M&W SmartCard 104
-
Java Card for the Internet of Things : ecure IoT Cloud Edge
A secure element running Java Card can play a critical role to ensure trust between the cloud and connected device. Find out how Java Card provides a secure local focal point for security policies
2021/07/19 M&W SmartCard 126
-
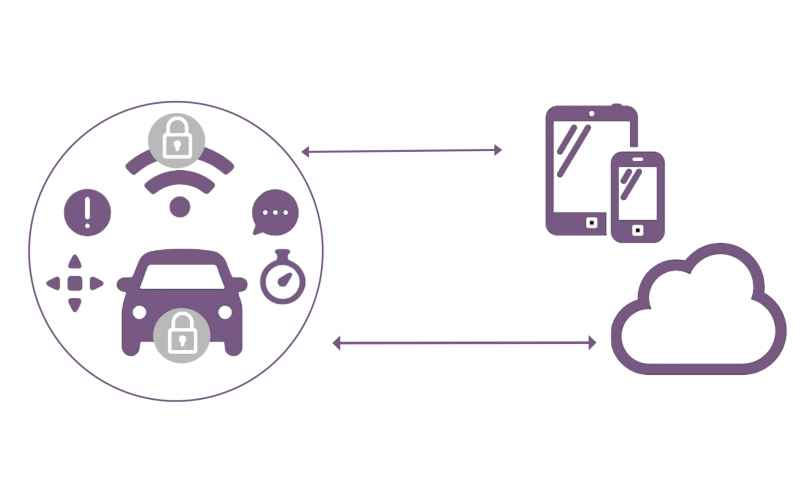
Java Card for the Internet of Things : Vehicle Communication Security
In a world of connected or even autonomously driving cars, privacy, integrity and confidentiality of the data exchanged must be paramount. Find out how Java Card based solutions can help to protect and manage the identities of vehicles
2021/07/19 M&W SmartCard 91
-
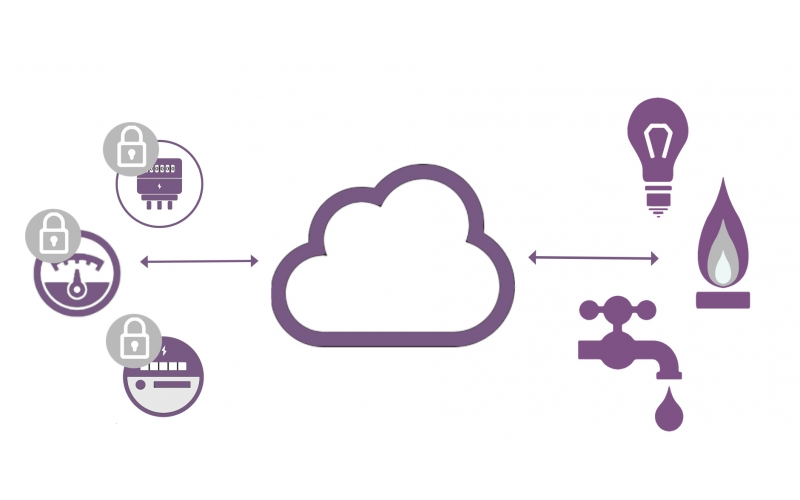
Java Card for the Internet of Things : Smart Metering and Smart Grid
Java Card products are widely used in metering scenarios to provide authentication and integrity services. Find out how Java Card can protect metering security credentials
2021/07/19 M&W SmartCard 76
-
Java Card for the Internet of Things : Secure Gateway Authentication and Communication
Java Card-based secure elements are a prime choice for implementing gateway security. Find out how Java Card ensures mutual device / cloud authentication
2021/07/19 M&W SmartCard 79
-
Java Card for the Internet of Things: Secure Network Access and Communication
Find out how Java Card provides the perfect environment to securely store credentials IoT device manufacturers deploy embedded SIM (eSIM) modules for consumer and M2M use cases to provide a reliable, robust and trusted access to the IoT ecosystem.
2021/07/19 M&W SmartCard 90
-
Checking and Signing XML Documents on Java Smart Cards- Challenges and Opportunities
CHECKING AND SIGNING XML DOCUMENTS ON JAVA SMART CARDSChallenges and OpportunitiesNils Gruschka, Florian Reuter and Norbert LuttenbergerChristian-Albrechts-University of KielAbstract:One major challen
2020/12/07 M&W SmartCard 76
-
NXP JCOP 4 Security Target Lite v3.4 12
The Security Functions (SF) introduced in this section realize the SFRs of the TOE. See Table 8.1 for list of all Security Functions. Each SF consists of components spread over several TOE components to provide a security functionality and fulfill SFRs
2020/07/14 M&W SmartCard 165